For most journalists, producing accurate, reliable reporting in the public interest is a daily job requirement, and one that is no more paramount than in times of crisis. Yet producing that reporting often demands that journalists rely on sources who may not be authorized to speak to the press.
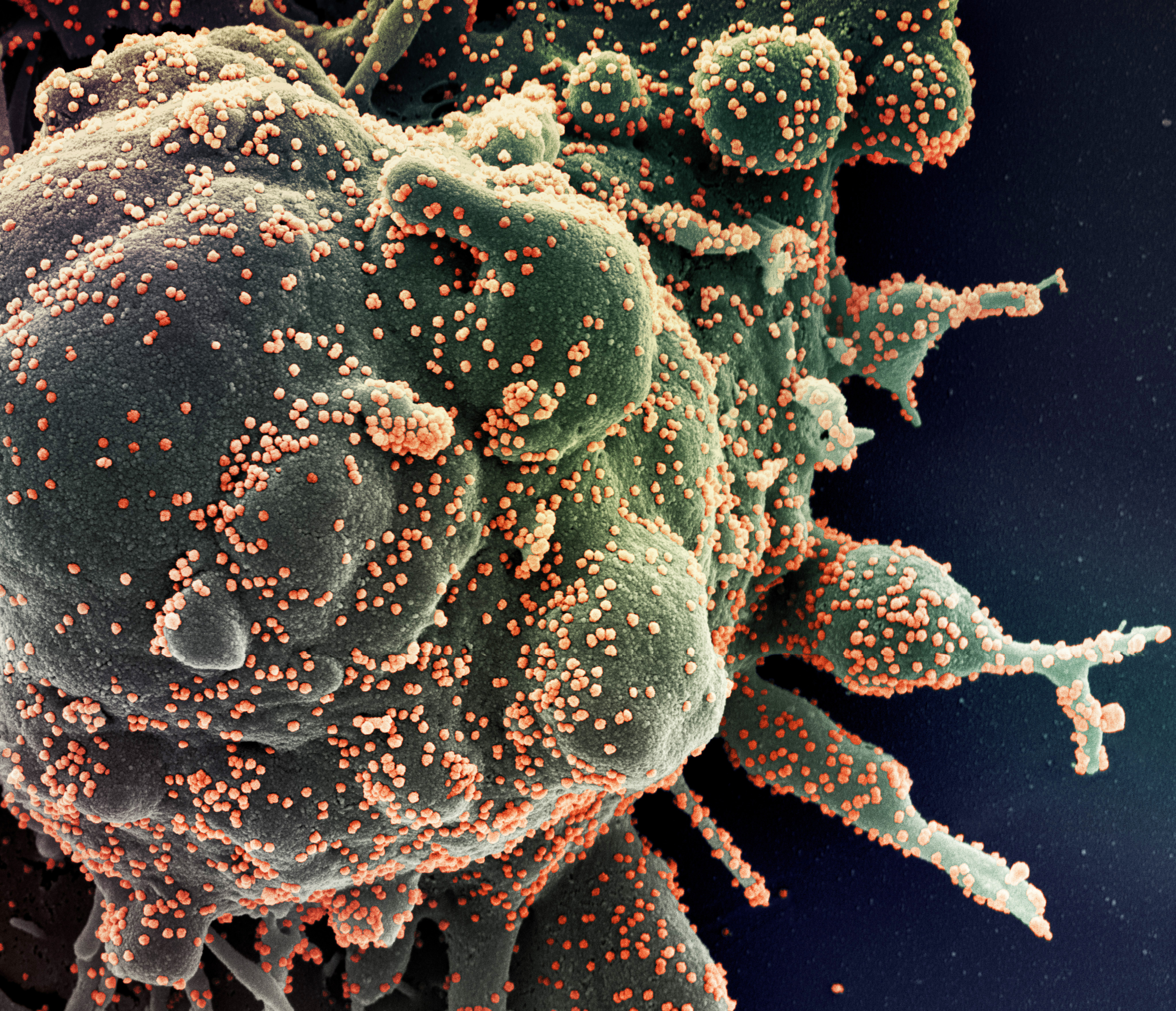
Working with such sources presents a particular challenge in the case of the current pandemic, when most journalists are being forced to conduct all of their work remotely. While these health precautions are crucial, journalists unused to an all-digital reporting process may be unwittingly putting themselves, their sources, and their work at risk in other ways.
Journalists often rely on face-to-face meetings to protect sensitive sources and materials; without this option, journalists’ communication choices matter more than ever. A particular challenge of covering the coronavirus pandemic is the relatively unusual nature of the threat it presents. In an interview with the Committee to Protect Journalists, Stefania Battistini, who works for Italian public broadcaster RAI and reported from the epicenter of the Italian crisis, highlighted that, unlike of bombings in a war zone, coronavirus is “invisible.”
“You do not have a physical connection to it,” Battistini said, “you only experience its consequences.” Because of this, WSJ disaster reporter Erin Ailworth told Poynter, reporting on the virus means “you have to treat the field as a place of constant exposure risk and protect yourself accordingly.”
In many ways, these persistent risks mirror those to already faced by journalists in the online environment, where missteps in protecting sources and information can have long-term consequences that are “invisible” in the moment. Below are some of the issues and approaches that reporters and newsrooms should consider as they move forward with remote-only coverage.
Protecting Sources
One type of protection for vulnerable sources is anonymity, but journalists must recognize that this term means something very different in the newsroom than it does in the context of technology. When it comes to digital communications, true anonymity exists only when the parties (or devices) that are connected cannot technically be traced; this high bar is impossible with apps and services that typically require a phone number or email account, meaning sources that go unnamed in a story could still be identified later through technical means. For example, the metadata generated by the use of these services—i.e. when and how frequently one party speaks to another, and for how long—is precisely what was used to prosecute Jeffrey Sterling, James Risen’s alleged source for his book State of War. This means that even relying on encrypted services is insufficient when true anonymity is what you really need.
There are only two strategies for trying to protect sources that might be at risk for even speaking to you: first, you can look to services like Jitsi Meet (https://meet.jit.si/), which creates ephemeral, browser-based video chats that don’t require any accounts or device information. Instead, the service creates randomly-generated room names which exist only for the length of your call, so the only way for an outsider to know who communicated is to know the room name you’re using and also connect to while your call is going on. This approach still suffers from the so-called “first contact” problem, however: you need a way to let your source know the URL of your chat room and when to “meet” you there. In ordinary circumstances, this could be done through a note, a letter or even word-of-mouth. If you want to pursue at the moment, your best bet might be to call a general number (of a hospital, say) and share the information about your room. After that, you’ll just have to hope it ends up in the right hands.
A more intuitive approach may simply be to create so much “noise” in your communication patterns that identifying your particular source becomes nearly impossible. This means communicating securely (via an encrypted phone or messaging service) with many people who could credibly be the source for potentially sensitive information, being sure to contact all of them with about the same frequency and duration—for example, a daily 5-minute phone call or exchanging 20 messages per day with a group of several credible sources. Otherwise, the metadata about your communications with a source can quickly reveal about your relationship with them, even if the contents your exchanges are protected by encryption.
When it comes to choosing how to connect, most of us will to rely on whatever tool is most comfortable and accessible for our sources. Since the metadata about who you are communicating with is always accessible to a service provider (and is not protected by privacy laws, at least in the US), journalists will want to protect the contents of communications (e.g. the calls and messages themselves) as much as possible.
Start by choosing tools and platforms that encrypt the contents of your exchanges. In almost all cases, this rules out email altogether. Instead, opt for voice and messaging apps that support “end-to-end” (E2E) encryption; this means that even the service provider/owner can’t see the contents of your exchange. Tools like Signal, iMessage and WhatsApp are E2E by default; platforms like Facebook Messenger and Skype can support it, but you will have to review your messaging configuration to make sure it’s enabled for a given conversation.
From a journalistic perspective, video interviews may be preferable to chat and voice-only options, but be aware that true E2E video is very difficult to implement. Most video services—including Zoom, Google Hangouts, BlueJeans, and Wire—rely on a protocol called WebRTC, and end up effectively disabling E2E in order to improve call quality. Exceptions are Whereby, which does use E2E video for free accounts, as does Google’s Duo; Apple’s FaceTime also promises E2E encryption, but the implementation has not been independently reviewed. Jitsi also uses WebRTC but does not offer E2E encryption; it’s protection comes primarily from the ephemerality of its connections and fact that it doesn’t require downloading an app or registering an account.
If you can’t use an E2E encrypted platform, you’ll need to decide which companies and platforms you or your sources trust most before choosing them, as almost any service provider could technically view your calls. If you can make do with a voice-only connection, many E2E “chat” apps also support phone calls, and even an old-fashioned telephone call can be a good option, since obtaining a wiretap authorization is (generally) time-consuming and legally complex.
Protecting Intra-Office Communications
The good news for organizations already relying on cloud-based services is that a move away from the newsroom will not do much to disrupt many regular workflows. At the same time, when reporters are working from wherever they can, it becomes even more essential that access to their accounts is properly secured. If they haven’t already, organizations should make non-SMS (read: app- or “security key”-based, rather than numeric codes texted to your phone) multi-factor authentication on all work accounts mandatory. This is also a good time to start using a password manager (1password, for example, offers free accounts for journalists), which not only generate and autofill strong, unique passwords across devices, but make it extremely simple to securely share those passwords among team members. As remote work requires all of us to adapt to new roles and responsibilities, this latter feature is increasingly important: new team members can be given access to as many accounts as needed with a single email invitation. At the same time, editors can see at a glance who has access to what, and prune access with the click of a button if needed.
Fully remote work also removes the opportunity for colleagues to have sensitive conversations face-to-face, meaning some of those conversations could end up on relatively insecure platforms, like Slack. Editors and newsroom managers will want to think carefully about how they configure their intra-office communications to limit the potentially sensitive material that moves through these channels. Keybase provides encrypted group messaging and file sharing, and setting up groups on encrypted chat apps (like Signal or WhatsApp) can meet some of the same goals. If you absolutely must stay with Slack, Freedom of the Press Foundation has an excellent set of of guidelines for making your team’s conversations as private as possible.
Protecting Yourself
In the last few years, harassment, “doxing,” and reputational attacks have quickly become the most common and significant security risk for journalists and news organizations. Social media platforms are often a key mechanism for carrying out these attacks, and their tools for mitigating such attacks are piecemeal at best. Journalists at large organizations can and should notify their security personnel if they are targeted, but many significant protections can (and must) be implemented by journalists themselves:
- Separate the personal from the professional. This goes for email addresses and social media accounts. Don’t auto-forward emails from one email account to another, and don’t post personally revealing information (e.g. photos of your home, children, daily commute) to your professional social media accounts. This doesn’t mean that your professional accounts should be dry or boring, only that information that could be used to identify your physical whereabouts and/or your close friends and family members should never be posted on an unprotected profile. In fact, close friends and family should avoid even following you on these public profiles, especially on “real name” networks like Facebook, where attackers can target loved ones as a way to reach you. Instead, make fully protected profiles and ask those close to you to follow you there. While you’re at it, you may want to review your existing posts and remove any that share too much, or even set your public posts to auto-delete (if applicable, talk to your editor first).
- Get a “work only” phone number. If you don’t have a company mobile number, you can do this through services like Google Voice or paid apps like Sideline; the key feature you’re looking for is a distinct phone number so that being away from the office doesn’t mean handing out your personal number to every source you want to reach. Mobile phone numbers are highly identifying; having yours easily accessible can make account takeover and even identity theft much easier for attackers.
Walter is OUTSIDE pic.twitter.com/ePTqhwBSwP
— Jessica Huseman (@JessicaHuseman) April 9, 2020
(NB: Huseman notes further down that her dog is wearing her work number) - “Dox” yourself—and then get that information removed. This can be an unsettling and time-consuming process, but knowing what information about you is on the web is the first step to getting it removed. Go through old accounts and services (like that long-lost Tumblog) and deactivate or delete them; if you want to keep them alive, at least strengthen the password and add multifactor authentication if possible. Getting your data removed from so-called “people finder” sites, which often refresh data annually from public records, is more involved. You can either make use of their “opt out” processes, or pay a service like DeleteMe to do it for you. Either way, the results are neither immediate nor perfect, but can do a lot to protect you in the case of online attacks.
- Freeze your credit. In addition to getting your free annual credit report and checking for unexpected accounts, be sure to remove any out-of-date phone numbers or addresses. You’ll also want to freeze your credit, which you can do for free at all major credit bureaus. While you will need to actively unfreeze your credit in order to obtain a loan or credit card, this process is also free and well worth the effort, since it helps block a major mechanism of identity theft.
Emotional well-being and self-care
Fortunately, a wide range of journalistic organizations and communities are actively talking about self-care during this crisis. The Dart Center for Trauma has a deep library of resources available, and the Online News Association is also curating Community Circles to help journalists connect to one another. Even commercial companies like Headspace, a meditation app, are offering collections of free resources. If you don’t have one already, this is precisely the moment to begin creating a self-care routine, using whatever resources and networks work best for you.
Protecting Your Stories
For months, the World Health Organization has been warning of a social media-driven “infodemic” related to the novel coronavirus, with the United Nations working with major platforms and search services to help vet information sources and highlight reputable information sources.
While these efforts are essential for the general public, journalists in particular need to be on the lookout for escalated efforts to manipulate their reporting or piggyback on their social media posts to spread dis- and misinformation. Fortunately, additional fact-checking resources centered around coronavirus are a helpful complement to existing best-practice advice for verification practices from sources like First Draft News.
While there is no such as perfect security, being informed and methodical about how you handle digital communications and information is ultimately your best defense against the vast majority of otherwise “invisible” online risks. No matter how many (or how few) of the recommendations above you’re able to adopt, know that in doing so you are taking concrete steps to protect your sources, your organization, yourself and your work – not just during this crisis, but well into the future that follows.
Has America ever needed a media defender more than now? Help us by joining CJR today.